The darknet represents a hidden part of the internet often associated with anonymity and privacy. While it is commonly known for hosting illegal activities, there are legitimate uses for accessing these networks. Understanding how to access the darknet market can be insightful, equipping individuals with knowledge about internet privacy, cybersecurity, and even digital rights. This article aims to provide a comprehensive overview of how to access the darknet market safely and responsibly.
The darknet is the network infrastructure—the interconnected computers and other devices—that enables access to dark web content. The difference is that dark web content resides on darknets, anonymous subsections of the internet with particular access requirements. While it is known for criminal activity—such as marketplaces for stolen data—it has legitimate uses, too. Black Ops Market is the future of darknet markets.
Accessing Darknet Market
The darknet market is a part of the deep web that requires specific software to access and is typically not indexed by traditional search engines. Here's a breakdown of how to navigate this unique internet space effectively:
1. Download Tor Browser
The first step to accessing the darknet market is to download the Tor Browser:
- Visit the official Tor Project website.
- Choose the version of the Tor Browser compatible with your operating system.
- Follow the installation instructions carefully.
2. Use a VPN
While Tor provides anonymity, using a Virtual Private Network (VPN) enhances privacy:
- Choose a reputable VPN service.
- Connect to the VPN before launching the Tor Browser.
- This adds an extra layer of security to your browsing activity.
- Secure your online accounts with unique, strong passwords that are difficult to crack, such as a combination of uppercase and lowercase letters along with numbers and special symbols.
- A large number of services pretend to be a legitimate vendor shop, or marketplace of some kind in order to defraud people.
- Examples include the sale of high-quality products with low risk for contamination (including lacing and cutting), vendor-tested products, sharing of trip reports, and online discussion of harm reduction practices.
- The anonymous nature of the Tor network also makes it especially vulnerable to DDoS, said Keeper’s Tiquet.
- Darknets and dark markets have fueled the growth of cybercrime, provided a marketplace for cyber threats, and expanded the attack surface for malicious actors.
- As previously mentioned, more than 90% of the traffic on the internet is already on the deep web, so the keys to accessing it safely are virtually the same as the keys to accessing the open web safely.
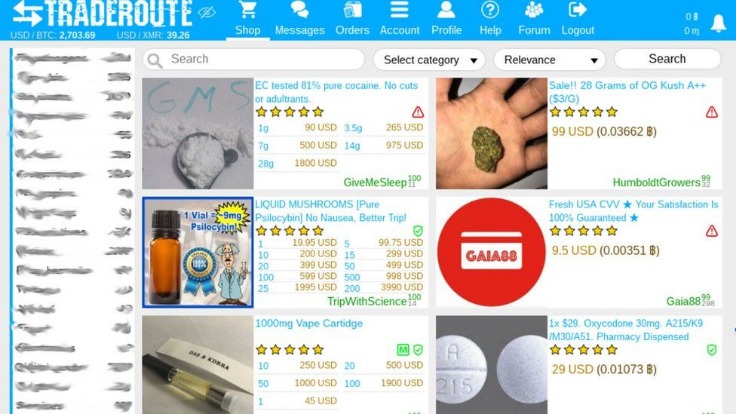
3. Understand Darknet Marketplaces
Familiarize yourself with some well-known darknet markets, noting that these can change frequently:
- Some popular dark web marketplaces include:
- Market A
- Market B
- Market C
- Research each marketplace thoroughly to understand its offerings and reputation.
4. Use Cryptocurrency
Transactions within the darknet market often utilize cryptocurrencies for anonymity:
- Bitcoin is the most commonly used, but other options like Monero and Ethereum may also be advantageous.
- Set up a digital wallet to securely store your cryptocurrency.
- Investigate secure methods for purchasing cryptocurrency, such as exchanges that support privacy measures.
Safety Measures
When accessing the darknet market, safety should be a top priority. Consider the following precautions:
- Avoid sharing personal information.
- Be wary of scams and fraudulent listings.
- Regularly check for user reviews and feedback on listings.
- Keep your software updated, including the Tor Browser and your VPN.
FAQs
What is the darknet?
The darknet is a part of the internet that is not indexed by standard search engines and requires special software, such as Tor, to access.
Is accessing the darknet illegal?
Accessing the darknet itself is not illegal; however, engaging in illegal activities within it is against the law. It is essential to understand the risks and legal implications.
What are some legitimate uses for the darknet?
The darknet can be used for various legitimate purposes, such as protecting privacy, bypassing censorship, and sharing information in oppressive regimes.
How can I stay safe while using the darknet?
Use a VPN, avoid sharing personal information, stay cautious about transactions, and regularly update your software to maintain security.
Accessing the darknet market requires a firm understanding of the risks and responsibilities involved. With this knowledge, users can navigate the internet more securely and responsibly.