The darknet is often surrounded by mystery and misconceptions. While it can be a platform for illicit activities, it also serves as a space for privacy-conscious users seeking information safely. For those wondering how to access darknet on Android, this guide aims to provide clear, educational steps to ensure a safe and secure experience.
Access Darknet On Android
- Both the people visiting dark websites and the people hosting them cannot be easily identified.
- After you save a Snap or Story to Memories, you can move it to My Eyes Only.
- Hackers can churn through billions of guesses per second, making light work of all but the strongest passwords.
- The OnionScan program, written by independent security researcher Sarah Jamie Lewis, comprehensively examines onion services for such flaws and vulnerabilities.
Review the details below to see where your data was exposed. This email address has been found in multiple data breaches. Timeline of data breaches affecting your email address Lewis points to the "first contact problem", when an attacker spots when someone moves from non-private tools to private ones, noting it's been used to identify whistleblowers. "And if I use Tor then I have a good degree of certainty that at least the local weirdos are not looking over my digital shoulder at what I am browsing — and that when I kill my browser (unless I've bookmarked something, or saved a file) then all the data is properly cleaned-up and wiped." "The big win of Tor for me is access — with a sprinkling of anonymity, to be sure — but that I can be stuck behind some hotel firewall, in some airport or restaurant lounge, or in a sketchy cafe is a sketchy country," Muffett says.
To access darknet on Android, it's essential to understand the tools required and the steps to take. This enables users to surf the web with a degree of anonymity and security, protecting their sensitive information from intrusive surveillance.
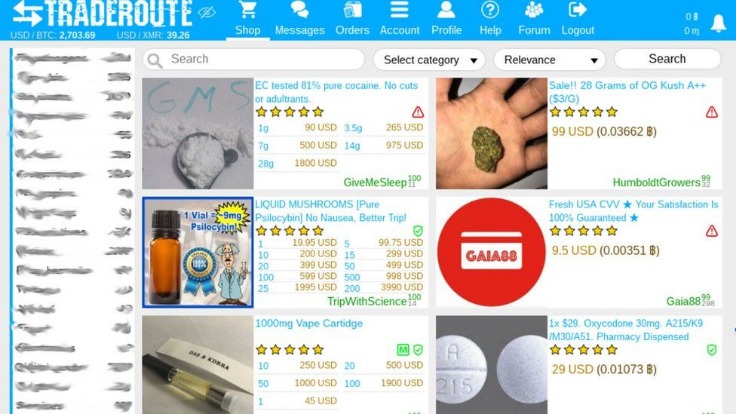
The dark web isn’t dangerous because it’s dark; it’s dangerous because it’s unregulated. It’s convenient for quick dark web access, especially for beginners who don’t want to install separate software. Like Tails, Subgraph is a secure Linux-based OS built for anonymity. It’s extremely secure, but not beginner-friendly browser. It supports its own .i2p sites and encrypted peer-to-peer communication. It is an anonymity-focused network, though more niche than Tor.
1. Understanding the Darknet
The darknet comprises parts of the internet not indexed by traditional search engines. It can be accessed through specialized software, where users often utilize anonymity networks like Tor. Understanding this privacy-focused network is crucial before diving in.
- Dark web monitoring is the process of searching for, and tracking, your organization's information on the dark web.
- Some websites claim to offer “online dark web access” through proxies or Tor gateways, but these come with risks.
- Some surface websites—such as Facebook—even have official dark web versions.
- Tor66 combines traditional search with a categorized directory of .onion sites.
- There are a lot of these sites across the dark web, which is why you have to be extra careful.
- A lot of the user data that gets stolen or leaked from big platforms ends up on the dark web, where users buy, sell, and exchange it among themselves.
2. Downloading the Necessary Apps
For Android users, the most popular app to access the darknet is the Tor Browser. It routes your connection through various servers, ensuring anonymity. Follow these steps to download and install:
- Visit the official Tor Project website to download the Android version of the Tor Browser.
- Enable installations from unknown sources in your device settings.
- Install the app, making sure to verify its authenticity via trusted sources.
3. Connecting to the Tor Network
Once the Tor Browser is installed, launch it to connect to the Tor network. This may take a few moments. After connection, you're ready to browse the darknet.
4. Ensuring Your Security
Security should always be a primary concern. To further protect your identity while browsing:
- Use a Virtual Private Network (VPN) in conjunction with the Tor browser for an added layer of security.
- Disable JavaScript in the Tor settings to minimize vulnerabilities.
- Be cautious with the information you share and the sites you visit.
5. Navigating the Darknet
When exploring the darknet, you'll discover a unique browsing experience. Accessing .onion sites, which are exclusive to the Tor network, is common. These websites often have a different look, and many provide vast information not available on the surface web.
6. Understanding the Risks
While the darknet can be a haven for privacy, it is crucial to remain aware of the potential dangers. Illicit activities can take place, thus it's wise to navigate judiciously and avoid engaging in any illegal conduct. Understanding the boundaries of law in your region is essential while browsing.
Conclusion
In summary, accessing the darknet on Android involves a series of straightforward steps that focus on anonymity and security. By using the Tor Browser and implementing best practices, users can explore the darknet safely. Always stay informed and cautious to make the most of your experience while respecting the law.