The world of cybersecurity is constantly evolving, and with it comes a range of terms and concepts that every individual should be aware of. One such term that has gained attention in recent years is 0day onion. This concept merges two critical aspects of technology: zero-day vulnerabilities and the anonymity provided by the Tor network, often referred to as "onion routing." Understanding how these components interact is crucial for users who want to protect themselves in an increasingly complex digital landscape.
What is a 0day Vulnerability?
A zero-day vulnerability is a security flaw in software that is unknown to the vendor or developer and, therefore, has not yet been patched or addressed. Attackers often exploit these vulnerabilities to gain unauthorized access to systems, steal data, or deploy malicious software before the developers can respond. The term "zero-day" refers to the fact that the developers have had zero days to fix the vulnerability since its discovery.
Understanding Onion Routing
Dining cryptographer networks have much lower latency but scale very poorly. One reason why it's not devastating to the network as a whole is that the process for getting your relays to make up such a large fraction of the network is social. I understand that they have mechanisms preventing obviously fake new servers from flooding the network. This makes them very different than known but still unpatched vulnerabilities. Which was/is more relevant when commercial software is updated at most once ever year or two I kind of feel like we just use 0-day to mean big problems, everything else is just a bug that has some age, and then fixed stuff doesn't get remembered.
Onion routing is a technique for anonymous communication over a computer network. It encrypts data in layers, similar to the layers of an onion, and routes it through a series of volunteer-operated servers, known as nodes. This process obscures the source and destination of the data, providing users with a high level of privacy online. The most popular implementation of onion routing is the Tor network, which allows users to browse the internet anonymously.

The Intersection of 0day Vulnerabilities and Onion Routing
- These vulnerabilities, unknown to the software vendor and thus lacking any patch, are procured through private research, covert teams, or cybercriminal infiltration.
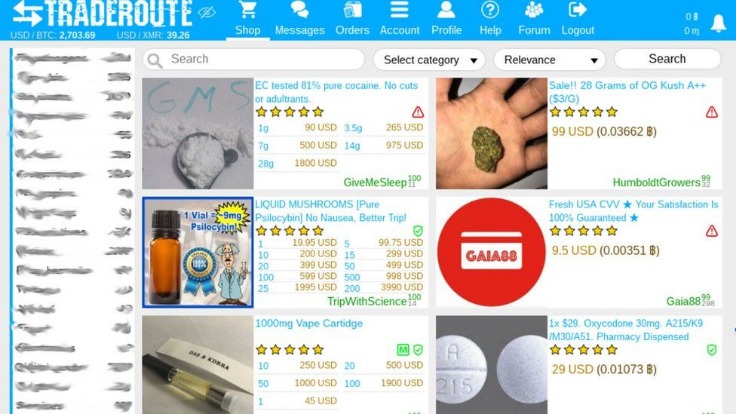
- The emergence of platforms like 0day onion underscores the increasing complexity of tackling illicit activities conducted anonymously through encrypted networks and dark web domains.
- Users here are often involved in various aspects of cybersecurity, sharing knowledge about the latest hacking tools and methods to exploit software weaknesses before developers can patch them.
- Bunching onions (also called scallions or green onions) don’t form bulbs like traditional onions, and typically mature in 60 days or less.
- As technology evolves, so does the need for robust security measures to protect against these sophisticated attacks.
When we talk about 0day onion, it often refers to the possibility of utilizing zero-day vulnerabilities within the anonymity of the Tor network. Attackers can exploit these vulnerabilities while maintaining their anonymity, making it challenging for cybersecurity professionals to track and mitigate threats. This combination poses a significant risk, especially for those who engage in activities that may attract unwanted scrutiny.
Why Awareness Matters
For individuals and organizations alike, understanding the implications of 0day onion vulnerabilities is essential. Armed with knowledge about these security threats, users can take proactive steps to protect themselves. This includes using reliable security software, keeping systems updated, and practicing safe browsing habits. Awareness can often be the first line of defense against potential exploitation.
How to Stay Informed
To navigate the complexities of the digital landscape, it’s vital to stay informed about the latest cybersecurity trends and threats. This can include subscribing to cybersecurity newsletters, engaging with online communities, and attending workshops or seminars focused on digital security. The more informed individuals are, the better equipped they will be to recognize and respond to cybersecurity threats, including those stemming from 0day onion vulnerabilities.

Conclusion
In conclusion, the intersection of zero-day vulnerabilities and onion routing encapsulates a significant aspect of modern cybersecurity risks. Understanding 0day onion is crucial for anyone who wants to safeguard their digital life. By staying informed and adopting best practices in cybersecurity, individuals can protect themselves from potential exploits and enhance their overall online security posture.