The dark web, a part of the internet not indexed by traditional search engines, has intrigued many with its veil of anonymity and mystery. While it is often associated with illegal activities, the dark web also plays host to discussions, communities, and resources that operate outside of mainstream awareness. Understanding how to access the dark web responsibly can be both informative and potentially life-saving, as it equips individuals with knowledge about online safety, digital privacy, and even necessary resources in critical situations.
The Dark Web is a segment of the Deep Web, which typically hosts illegal affairs, but not everything on it is illegal. However, it is reasonable to know your content and ensure proper authorization. Users of the dark web might face severe trouble with scams, legal issues, and threats against their safety. Understanding the differences between the deep web vs dark web is crucial for the safe and responsible use of the internet.
What is the Dark Web?
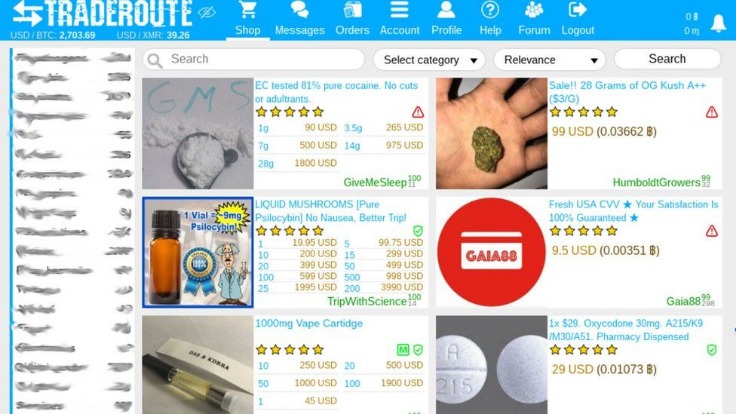
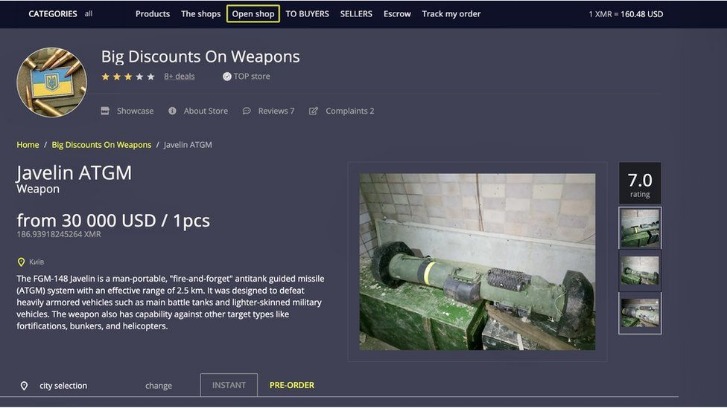
The dark web, which is great for privacy, harbors significant risks that stem from its very nature of anonymity and lack of oversight. The impact of these activities can extend beyond the direct participants, affecting community safety and societal trust. The dark web hosts a range of criminal activities that can have direct and indirect impacts on individuals and businesses. Understanding these threats is crucial for anyone venturing into the dark web, as it prepares them to take proactive measures for dark web protection and to safeguard their digital assets. Navigating the dark web comes with inherent risks due to its anonymity and lack of regulation. Understanding these distinctions is crucial for employing robust dark web protection and security.
To comprehend how to access the dark web, it is essential to first understand what it is. The dark web is a segment of the internet that requires specific software, configurations, or authorization to access. It operates on an encrypted network and is intentionally hidden. Unlike the surface web, where most online activities occur, the dark web uses anonymity tools to protect its users' identities and locations.
While Tor browsers are used to access the dark web, search engines play a crucial role in facilitating the browsing experience for users. These networks each operate differently but share the goal of protecting anonymity and providing access to unindexed online spaces. The deep web consists of unindexed content not accessible via standard search engines. This is the publicly accessible portion of the internet that can be indexed by search engines. The darknet is the underlying network infrastructure—overlay networks built on top of the standard internet that require specific configurations or tools to access. Nevertheless, users can also use the Tor network to mask illegal activities, which makes it a prime target for law enforcement and hackers.
How to Safely Access the Dark Web
Entering the dark web requires careful preparation to ensure your safety and privacy. Follow these steps to navigate it responsibly:
1. Use a VPN
Before accessing the dark web, it's crucial to install a reliable VPN (Virtual Private Network). A VPN encrypts your internet connection and masks your IP address, providing an extra layer of security.

2. Download Tor Browser
The Tor Browser is the primary gateway to the dark web. It routes your internet connection through multiple servers, enhancing privacy. Download Tor from its official site to avoid malicious versions.

3. Adjust Browser Settings
Once Tor is installed, adjust settings to enhance security. Disable scripts and active content to protect against potential exploits on malicious sites.
- Essentially, the deep web hosts protected or gated content requiring specific credentials (like login details) for access.
- The kinds of content present in this region include private databases, medical records, academic journals, and other sensitive information that requires special permission to access.
- Organizations monitor the dark web to track stolen credentials, leaked sensitive information, malware campaigns, and zero-day vulnerabilities.
- To most users, the internet is what they experience through their email client and web browser every day, but there are a number of expansive services that operate in the background and the “web” is just one part of it.
- The many layers of an onion represent the multiple layers of encryption in the Tor network.
4. Use Trusted Links
Many sites on the dark web are notorious for scams or illegal activities. It’s essential to have a list of trusted ".onion" links, which are the addresses used on the dark web, to navigate safely.
Navigating the Dark Web: What to Expect
When you access the dark web, the interface might appear unfamiliar. Websites can be slower due to TOR's routing processes, and the content often skews towards anonymity-oriented forums and marketplaces, alongside support resources for various communities.
Understand the Risks
Engaging with the dark web comes with its own set of risks, including exposure to illegal content, scams, and hacking attempts. It’s vital to approach it with caution, staying aware of the potential dangers that lurk online.
Utilizing Valuable Resources
Despite its daunting reputation, the dark web contains resources that can be beneficial. For instance, whistleblower sites allow individuals to disclose information confidentially, while forums may support those seeking help regarding sensitive issues, such as mental health or addiction.
Conclusion
Accessing the dark web can offer insights and connect individuals with valuable resources, but it should always be approached with caution and understanding. By following safety guidelines and recognizing the inherent risks, users can traverse this hidden part of the internet while safeguarding their identities and personal information. Whether for research, vigilance, or support, knowing how to access the dark web responsibly empowers individuals in our increasingly digital world.